Please Keep Your Belongings with You at All Times
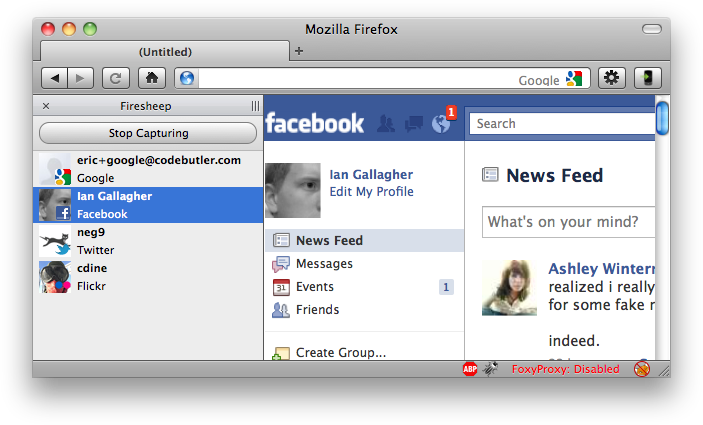
In case you missed it, a Firefox extension was released a couple of days ago called FireSheep. It's basically a simple, easy to use UI around a packet sniffer, allowing any user on an open wireless network to listen for authenticated HTTP requests from other users on that network, and use those to pose as them.
It uses an old technique, dating back to token ring or unswitched ethernet networks, when all packets passed through every node on the network, making it easy to grab them, but now it's a one-click install for anyone with a browser, specifically targeted at major social networking sites, and hijacking those connections seamlessly.
The author, Eric Butler, says:
Websites have a responsibility to protect the people who depend on their services. They've been ignoring this responsibility for too long, and it's time for everyone to demand a more secure web. My hope is that Firesheep will help the users win.
Eric isn't wrong. If all authenticated requests on the web used SSL, it would make packet sniffing and sidejacking impossible. In that sense, he's right.
But security is hard. Finding the balance between inconvenience and security is tricky. Facebook (to use an example) could issue card readers or fingerprint scanners, but they don't, because they figure that it would annoy their customers and the cost would be too high, relative to the potential risk.
The unspoken message is that your Facebook account is both not too important, nor too easy a target to require SSL for everything. Your bank considers your account to be at the other end of the scale - they use SSL, amongst other things, because it's an obvious target with a lot to lose if compromised.
But FireSheep has just changed the game. Your Facebook account is now a very easy target by any kid in your class at school. The relative easy of compromise means that it's a target, despite its relative unimportance.
(Side note: I wonder how prevalent FireSheep is at schools and universities at the moment.)
Given that this tool has received the attention it has, Facebook probably should make SSL mandatory, and I wouldn't be surprised if they did in the next couple of months (remember: it's harder than flicking a switch when you're at their scale).
Security isn't binary. Everything is insecure in some way, given enough effort.
What happens when the next tool comes out? Perhaps it pretends to be an access point of a similar name, or runs a rogue DHCP server on the same access point. It spoofs the DNS, and uses a self-certified SSL certificate (which most people will bypass) to proxy Facebook and the rest. I could probably write that in a long weekend, and have a post on Techcrunch on Monday.
And then maybe there will be some fuss, and eventually it'll die down, and maybe someone else will write another tool, using more advanced techniques (PDF).
Of course, forcing SSL doesn't add much inconvenience to users, nor is it a significant operations overhead for the services at risk, it's just that it's not the point here. The point is that making one-click tools that force the entire web to play catchup, whilst putting people at risk, just isn't a sensible way of talking about security.
There's a reason we (most of us, anyway) don't secure our houses with turret guns and dogs, and that's because most of the time, a lock and key is good enough. We want just enough security to feel safe at night, and not to cause us too much hassle.
And that's why this tool makes me sad. Because it's a symbol of an arms race - a fight to the death over unimportant things, when really, I'd rather not have to remember to lock my windows at night.